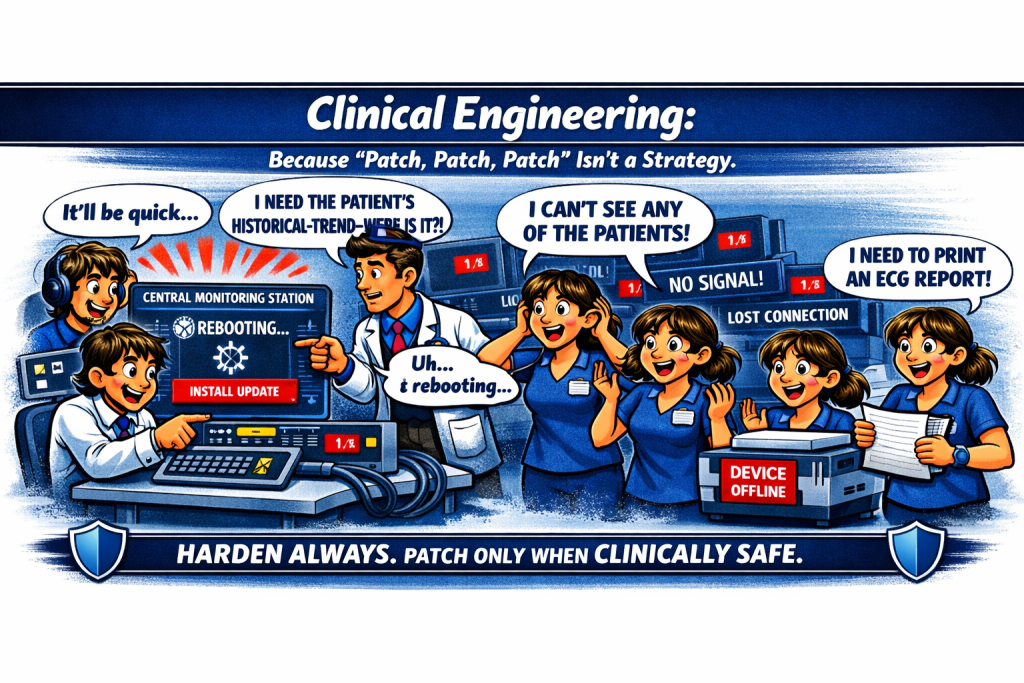
Why “Patch, Patch, Patch” Is the Wrong Advice for Medical Devices

In mainstream IT, “patch, patch, patch” is treated as gospel. It’s simple, catchy, and usually correct. But when this advice is applied to regulated medical devices, it becomes misleading and in many cases, non‑compliant with global standards.
In healthcare, it can create clinical risk, violate regulations, and jeopardise patient safety.
Medical devices are not general‑purpose computers. They are regulated, safety‑critical systems that support diagnosis, therapy, and continuous physiological monitoring. Many operate 24/7, where even a brief reboot is a patient‑safety event, not an IT inconvenience.
For these systems, clinical risk outweighs patch speed. Best‑practice frameworks across IEC, FDA, EU MDR, and NIST all agree:
Patching must be vendor‑validated, clinically safe, and risk‑managed – and compensating controls are the primary protection when patching is not possible.
24/7 Medical Devices Cannot Be Patched Like Normal IT Systems
Clinical uptime is non‑negotiable.
Devices such as patient monitors, ventilators, infusion pumps, and central stations run continuously.
A reboot, freeze, or driver conflict during patching can interrupt monitoring or therapy which is a direct clinical hazard.
This is why clinical safety > patch urgency.
IEC 80001‑1: Safety and effectiveness come first
IEC 80001‑1 requires healthcare organisations to maintain the clinical safety, effectiveness, and security of networked medical devices.
That means you must not:
- Apply patches that are not validated by the manufacturer
- Introduce downtime that disrupts clinical workflows
- Change software in ways that alter certified performance
Unvalidated or rushed patching violates the standard’s core principle:
Risk‑managed change, not speed‑driven change.
FDA & EU MDR: Software updates are regulated modifications
Under FDA and EU MDR, software updates on medical devices are regulated changes.
A vendor‑approved patch is only the starting point.
A compliant deployment requires:
- Vendor validation
- Local risk assessment
- Clinical leadership approval
- Safe downtime scheduling
- Compensating controls during the window
- Post‑deployment monitoring
The correct message is not “patch fast”.
It is: Apply vendor‑validated patches when clinically safe and harden continuously.
Many medical devices cannot follow a standard IT patch cycle
NIST SP 800‑82 and SP 800‑53 both recognise that in OT environments:
- Patching may be delayed
- Patching may be unavailable
- Patching may be unsafe
- Compensating controls must be used to manage risk
Medical devices often run:
- Vendor‑locked Windows Embedded builds
- Custom Linux kernels
- Real‑time operating systems (RTOS)
- Firmware that cannot be modified without regulatory impact
These platforms cannot accept patches at the same frequency as enterprise IT systems.
Compensating Controls Are the Primary Defence for Medical Devices
When devices cannot be patched, which is common, compensating controls are the safest, standards‑aligned approach.
Effective controls include:
- Network segmentation
- Protocol and port minimisation
- Access control and authentication hardening
- Jump hosts and isolation zones
- Continuous monitoring and anomaly detection
- Strict change control
- Physical security and workflow controls
These measures reduce cyber risk without touching the device, preserving clinical uptime and regulatory compliance.
This is not a workaround. It is the expected approach in IEC 80001‑1, NIST OT guidance, and FDA postmarket cybersecurity expectations.
The Real Strategy for Medical Device Cybersecurity
- Harden always.
- Patch when vendor‑validated AND clinically safe.
- Protect patients first.
For 24/7 medical devices, clinical risk is the governing factor, not patch velocity.
Compensating controls are not optional. They are the primary, safest, and most reliable method of risk reduction until a patch can be safely deployed.
Conclusion
Patch, patch, patch is wrong when you assume medical devices should behave like normal IT assets.
Patch, patch, patch is wrong when you overlook clinical safety requirements and the regulatory controls that govern these systems.
Patch, patch, patch is wrong when you apply a one‑size‑fits‑all IT mindset to a safety‑critical environment.
The goal of reducing cyber risk is entirely valid, but it cannot be applied effectively without a clear understanding of how this domain operates.
